Information security is still a neglected aspect in healthcare. The focus on security has been more compelled by regulations like NEN 7510, rather than driven by quality awareness and professionalism. Of course, the primary focus is on the patient. But the care for the patient should precisely lead to an interest in information security. We still too often experience incidents where hospitals have to close due to security breaches. All too often, patients’ privacy is violated, and healthcare institutions fail to meet the basic security requirements as defined in NEN 7510.
Patient care nowadays can no longer do without proper ICT and integrated attention to IT security. From the first contact with a patient or client, a healthcare institution collects various data. And with the latest technological advancements, not only does the amount of collected data increase, but so does the variety of methods through which this information is gathered, processed, and shared. To make it even more complex: medical data of patients and clients are inherently confidential and must always be reliable, no matter where or when. Effective information security in healthcare is therefore a matter of life and death!
Information security in healthcare must meet stringent requirements.
The advancing digitization and changing role of data also lead to the imposition of stricter requirements on information security. For example, health data constitutes a special category under the GDPR (General Data Protection Regulation). And it’s not without reason that working with NEN 7510 has been legally mandatory since 2018. This is because there is a high risk of incidents with significant impact.
Of course, as a healthcare institution, you also want to comply with the legislation. After all, you certainly don’t want to face fines. Security breaches and incidents can also lead to not only financial damage but also significant reputational harm. However, many healthcare institutions view the growing demands in data security and privacy as an additional hurdle. A hindering factor that necessitates the establishment of new processes and adds to the workload even further.
Information security actually contributes to excellent care and professionalism.
For those who see GDPR and NEN 7510 as bureaucracy, they will indeed find that they can be inhibitory. But you could also view information security in healthcare as a means to enhance the quality of patient care. NEN 7510 focuses solely on that. While it may not directly address the quality of healthcare provision, NEN 7510 does deal with information flows and the measures one must take to manage privacy and security risks. Indeed, accurate recording of medical data and effective information exchange do contribute to excellent care. Medical personnel must be able to trust that the necessary medical information is available, accurate, and complete. Moreover, everyone does value the protection of their own medical data, don’t they?
Start with patient care as the basis instead of regulations.
Exactly that should be the starting point for wanting to comply with NEN 7510. So, take these rules as an opportunity or a lever to enhance the quality of your patient care. Working with NEN 7510 genuinely contributes to a more effective and efficient way of providing healthcare. By viewing compliance with NEN 7510 as part of your quality policy, it becomes a strategic tool rather than a legal obligation. This also makes it more natural to strive for continuous improvement rather than rushing to get everything in order just before an audit.
IT service is a crucial foundation for working with NEN 7510.
Working according to NEN 7510 means that your organization is structured in a way that ensures information is well-secured and only accessible to authorized individuals. But it also means that the information is available and accurate at all times. These requirements pertain to the entire organization, but with increasing digitization, a significant portion of them is implemented through your IT service provision. And the quality of this service is determined by the execution of IT management. By organizing the approach of IT management effectively, you already largely comply with the established requirements. And fortunately, this can be achieved without additional hassle and new procedures.
‘Six Steps for Improved Patient Care through Integrated IT Management’
Incorporate NEN 7510 into your organization and your service levels.
Ensuring your information security according to NEN 7510 can be effectively achieved with a standard approach like the ISM method (Integrated Service Management). The advantage is that this method incorporates NEN 7510 into an integrated approach for effective service management, eliminating the need to establish separate processes. NEN 7510 and GDPR primarily impose requirements on IT service provision and are essentially nothing more than service levels that belong in Service Level Agreements (SLAs).
To comply with NEN 7510, an IT department must carry out activities related to the configuration of information systems and the department’s procedures. These activities are the same for every hospital and healthcare institution. You can effectively incorporate these activities into the fundamental work processes of the IT department. We have translated the NEN 7510 requirements into the necessary actions and linked them to the streamlined approach. You can then suffice with six streamlined ISM processes that cover your entire service management, including compliance with NEN 7510. This includes the setup, application, and assessment. You can also include requirements from the GDPR, as well as the Medical Technology Covenant and SLAs (Service Level Agreements) in this. Mandatory actions are no longer bureaucracy, as they are clearly linked to patient care.
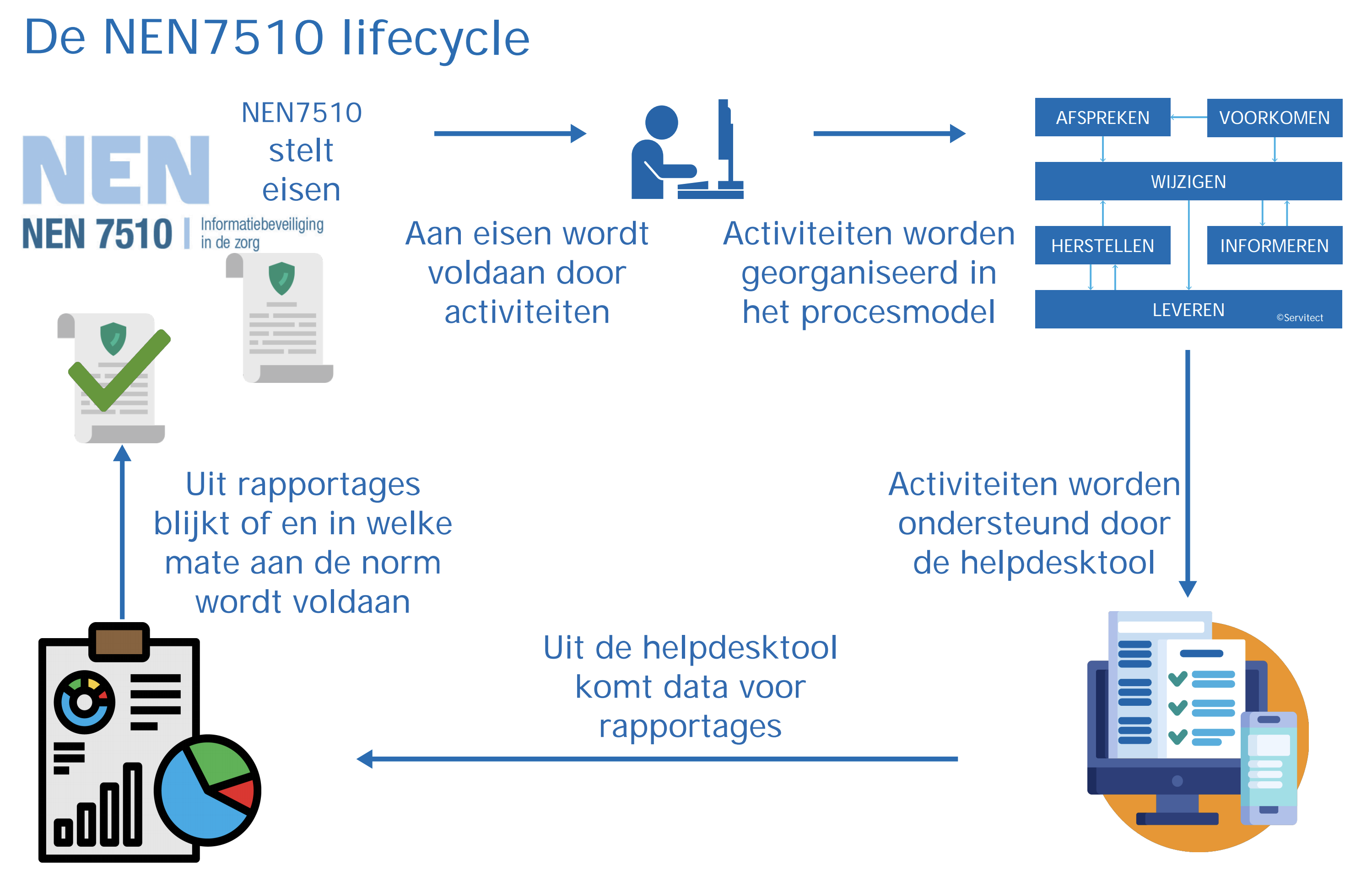
Furthermore, it’s important not only to have an updated assessment of compliance with NEN 7510 requirements after the annual audit but to maintain a continuous and current understanding of it. A NEN 7510 monitor can assist you in making strong information security a standard component of your policy and organization. In fact, this monitor is nothing more than a management model that allows you to know at any given moment where you stand in the NEN 7510 lifecycle. For example, at a glance, you can see which activities are adequately secured and which ones are not, as well as how close you are to achieving your goals.
Also, read our paper: ‘Meeting NEN 7510 Quickly and Sustainably.’
Information security in healthcare is the responsibility of everyone.
But information security in healthcare remains, of course, a responsibility of everyone in the organization. From management to the healthcare provider themselves. It is the responsibility of management to develop a robust information security plan at the strategic level, which forms the basis for the IT management approach at the tactical and operational levels. In addition, every individual employee must be aware of the importance of information security for the quality of healthcare provision. Even if digital privacy is well safeguarded, if medical personnel handle confidential data carelessly, you can still run into trouble.
Attitude and behavior of people remain crucial. Therefore, NEN has a handy NEN has therefore developed a convenient online awareness tool that provides healthcare professionals with feedback on their actions.
But effective information security only works if employees not only receive instructions but also understand the importance of certain procedures. And if they are continually informed about the current state of affairs. “Security is not just an action; it’s an attitude.” Only then does it become a matter of course. So, here too, the quality of patient care should be the starting point, not just compliance with rules. Customer value takes precedence above all else!
Demo compliance tool (advanced checklist)
Additionally, we have developed an online compliance tool for assessing and implementing NEN 7510. With this tool, you can easily navigate through the standards and requirements (an advanced checklist). With the associated and elaborated actions, you can seamlessly integrate them into your existing workflow. The phased implementation is supported by practical summaries and implementation forms.
Case study Dijklander Ziekenhuis
We have already assisted many organizations in implementing a streamlined, integrated approach. As a result, they have gained more control over their IT management and service management. Do you want to read how? Then download our case study from Dijklander Hospital.
If you want to learn more about the ISM method, download the free whitepaper with the ISM process model.